GBounty and GBounty Profiles Designer.
Website
Vulnerability
Scanner.
Fast, reliable, and highly customizable.
or discover more
Website scanner designed to find unique vulnerabilities.
GBounty is a standalone command line website vulnerability scanner developed in Golang designed to help companies, pentesters, and bug hunters identify potential vulnerabilities in web applications. Some of the key benefits include:
- Fast: GBounty is designed to identify potential vulnerabilities in web applications more quickly, saving you time and effort.
- Reliable: GBounty uses different types of scans (active and passive) to perform a comprehensive analysis of the target website, ensuring that potential vulnerabilities are identified accurately.
- Customizable: GBounty allows you to easily implement and search for new vulnerabilities in a quick manner.
- Integrable: GBounty can be integrated into your CI (continuous integration) scans and run on Linux, Windows, and macOS systems.
- Valuable information collection: In addition to identifying vulnerabilities, GBounty can also collect valuable information that can be useful during manual pentesting, such as identifying vulnerable parameters, detecting software versions, and more.
With GBounty, you can quickly and accurately identify potential vulnerabilities in web applications, saving you time and effort. Try it out today and see the difference for yourself!
Please, see the Documentation section for more information.
Why GBounty?
Fast
It can help you to identify potential vulnerabilities in web applications more quickly.
Reliable
The different types of scans: active and passive, allow you to perform a complete analysis on the target.
Customizable
You can implement new vulnerabilities in few seconds, and then GBounty will take care of finding them for you.
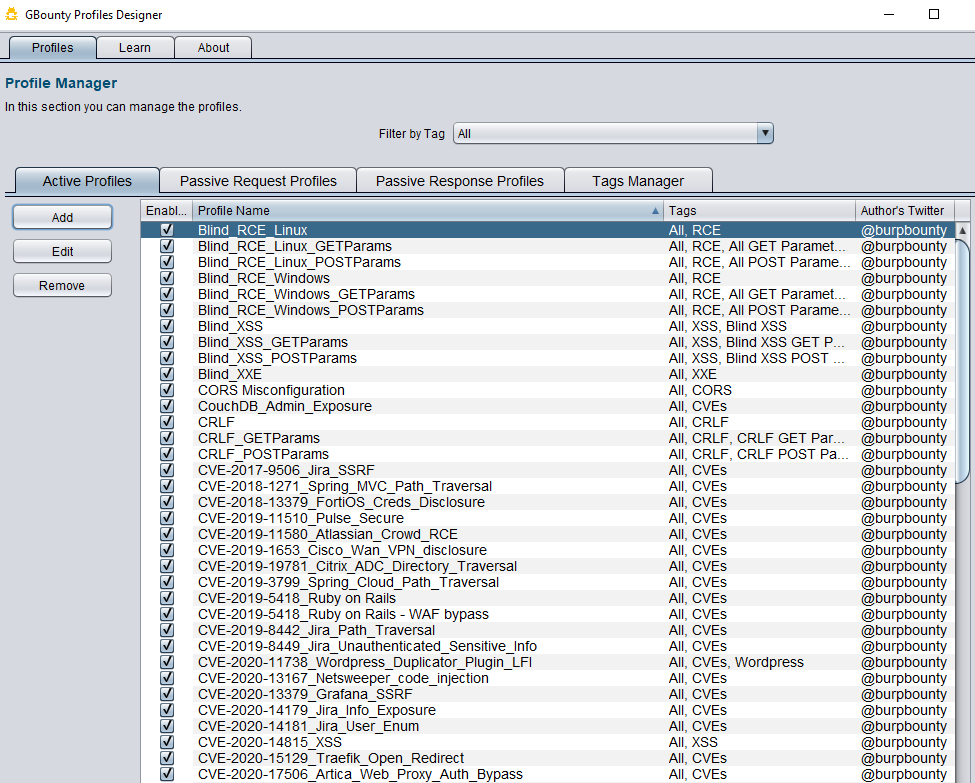
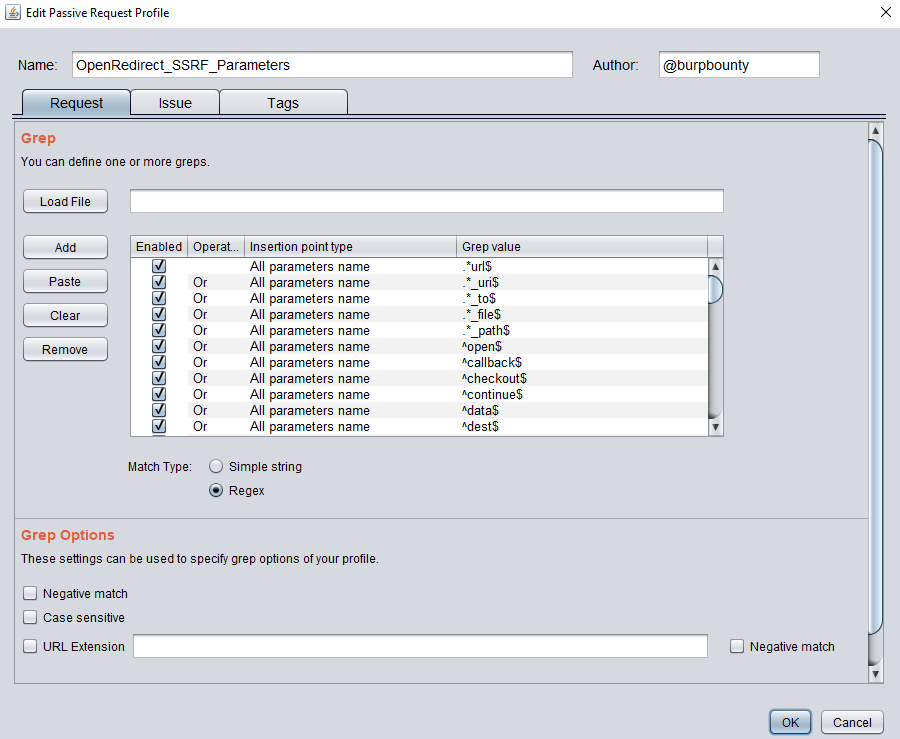
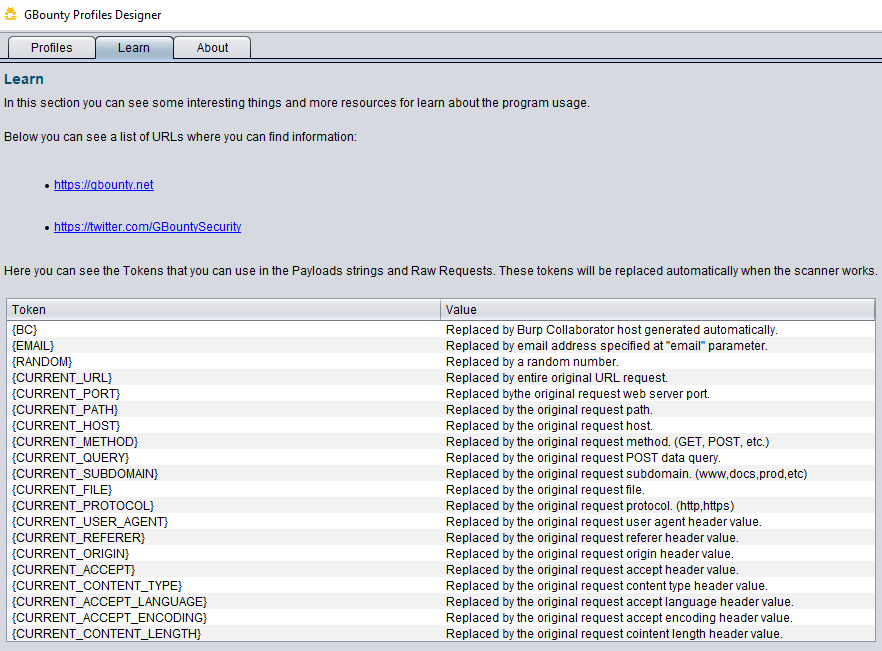
GBounty Profiles Designer.
GBounty Profiles Designer is a powerful tool that gives you the ability to create custom web vulnerability profiles for use with GBounty. Some of the key benefits include:
- Easy to use: It offers a graphical interface that makes it easy to create new vulnerability profiles.
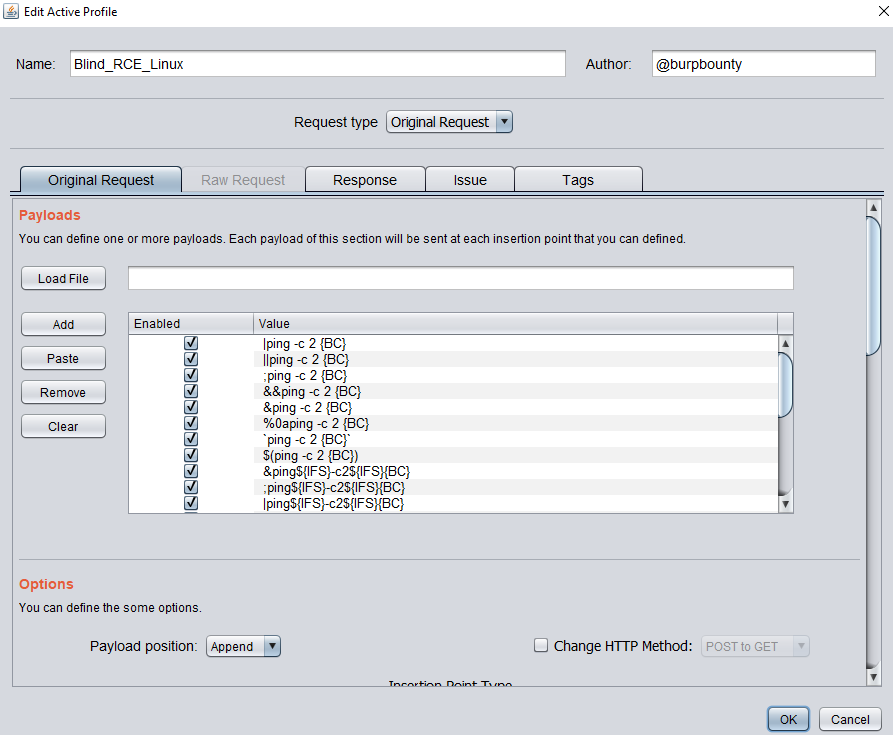
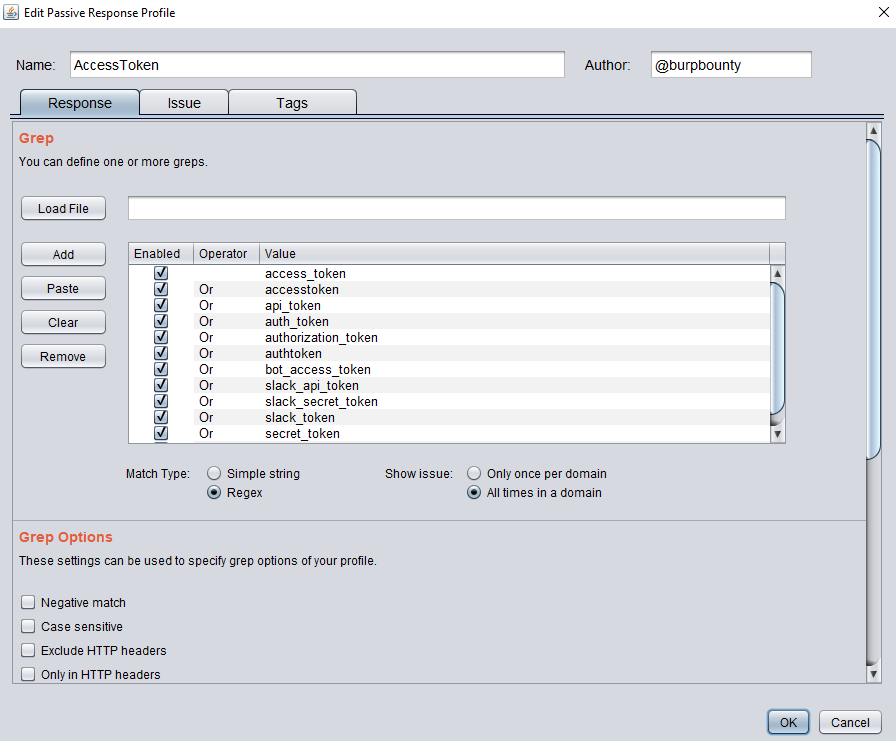
- Customization: It has a unique customization capacity, with new insertion points and search types that allow you to tailor the profiles to your specific needs.
- Passive and active profiles: You can create both passive and active vulnerability profiles, which can be used to perform a comprehensive review of a web application.
- Fast and efficient: It allows you to create new vulnerability profiles in a simple and fast way, so you can integrate new web vulnerabilities into your tests quickly.
Easy usage
The graphical interface it allows you to create new profiles in a few seconds.
Advanced profiles
More customizable web vulnerability profiles to control your scans.
More powerful
Extracting the insertion points from the requests, a in-deep analysis is ensured.
Better performance
Speed and efficiency in the web vulnerability scans are in our DNA.
Main clients.
These are some of our most recognized clients.
Testimonials